 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
Apple released emergency security updates to fix two new zero-day vulnerabilities exploited in attacks targeting iPhone and Mac users, for a total of 13 exploited zero-days patched since the start of the year.
"Apple is aware of a report that this issue may have been actively exploited," the company revealed in security advisories describing the security flaws.
The bugs were found in the Image I/O and Wallet frameworks and are tracked as CVE-2023-41064 (discovered by Citizen Lab security researchers) and CVE-2023-41061 (discovered by Apple). Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
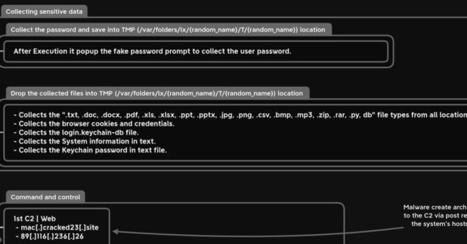
A new information stealer malware named 'MetaStealer' has appeared in the wild, stealing a wide variety of sensitive information from Intel-based macOS computers.
MetaStealer, not to be confused with the 'META' info-stealer that saw some popularity last year, is a Go-based malware capable of evading Apple's built-in antivirus tech XProtect, targeting business users. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
A security researcher caused something of a kerfuffle during the Def Con 2023 hacking conference in Las Vegas last month. Some attendees with iPhones were shocked to see an Apple pop-up notification asking them to connect to a nearby Apple TV device using their Apple ID credentials. Not least, as some of the hackers on the receiving end of these Bluetooth-powered prompts were running with Bluetooth disabled. Or so they thought. Now, another security researcher has demonstrated a similar hack that uses a readily available hacking device to spam nearby iPhones with pop-up notifications and effectively execute a denial of service attack. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
This is new. For the very first time, Apple has released a Rapid Security Response (RSR) update to iPhone users, with a corresponding RSR for the Mac. It represents a change in how Apple will launch smaller updates—as indicated by the number of this one. After iOS 16.4.1, you might legitimately have expected iOS 16.4.2 as the small update before iOS 16.5 lands.
But no, we now have a letter, and even parentheses, to attach to the numbers: here comes Apple iOS 16.4.1 (a). Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Apple’s latest update blast is out, including an extensive range of security patches for all devices that Apple officially supports.
There are fixes for iOS, iPadOS, tvOS and watchOS, along with patches for all three supported flavours of macOS, and even a special update to the firmware in Apple’s super-cool external Studio Display monitor.
Apparently, if you’re running macOS Ventura and you’ve hooked your Mac up to a Studio Display, just updating the Ventura operating system itself isn’t enough to secure you against potential system-level attacks.
According to Apple’s bulletin, a bug in the display screen’s own firmware could be abused by an app running on your Mac “to execute arbitrary code with kernel privileges. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Apple has backported security patches addressing a remotely exploitable zero-day vulnerability to older iPhones and iPads.
This bug is tracked as CVE-2022-42856, and it stems from a type confusion weakness in Apple's Webkit web browser browsing engine.
Apple said that the flaw discovered by Clément Lecigne of Google's Threat Analysis Group allows maliciously crafted webpages to perform arbitrary code execution (and likely gain access to sensitive information) on vulnerable devices. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
SAN FRANCISCO (AP) — Apple disclosed serious security vulnerabilities for iPhones, iPads and Macs that could potentially allow attackers to take complete control of these devices.
Apple released two securityreports about the issue on Wednesday, although they didn’t receive wide attention outside of tech publications.
Apple’s explanation of the vulnerability means a hacker could get “full admin access” to the device. That would allow intruders to impersonate the device’s owner and subsequently run any software in their name, said Rachel Tobac, CEO of SocialProof Security.
Security experts have advised users to update affected devices — the iPhone6S and later models; several models of the iPad, including the 5th generation and later, all iPad Pro models and the iPad Air 2; and Mac computers running MacOS Monterey. The flaw also affects some iPod models. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Here on Naked Security, we’ve been lamenting the mysterious nature of Apple’s security updates for ages.
For example, even when widely-known security problems appear in components that are part of Apple’s operating system, Apple routinely refuses to say when, or even if, it plans to address the issues itself. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Microsoft has detailed the evolution of a relatively new piece of Mac malware called UpdateAgent that started out stealing system information in late 2020 but has morphed into a tool for delivering adware and potentially other threats.
One of UpdateAgent's newest and most potent features is the ability to bypass Apple's built-in Gatekeeper system that is meant to allow only trusted, signed apps to run on Macs.
Microsoft flagged the malware now as it appears to be under continuous development. Today, it installs an "unusually persistent" adware threat called Adload, but Microsoft cautions it could be used to distribute other more dangerous payloads in future. For example, Microsoft found its makers host additional payloads on Amazon Web Services' S3 and CloudFront services. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Apple's latest iOS brings more than just a dubious Voice Plan to the table.
The company behind the iPhone released its latest operating system, iOS 15.2, Monday, and hot damn is it a doozy. The update includes 38 (thirty-eight!) separate privacy and security fixes in addition to its more flashy and hyped components — and you should really go ahead and download it. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
UK academics have uncovered mobile security issues in Visa and Apple payment mechanisms that could result in fraudulent contactless payments.
On Thursday, academics from the UK's University of Birmingham and University of Surrey revealed the technique, in which attackers could bypass an Apple iPhone's lock screen to access payment services and make contactless transactions.
A paper on the research, "Practical EMV Relay Protection," (.PDF) is due to be published at the 2022 IEEE Symposium on Security and Privacy, and has been authored by Andreea-Ina Radu, Tom Chothia, Christopher J.P. Newton, Ioana Boureanu, and Liqun Chen.
According to the paper, the 'vulnerability' occurs when Visa cards are set up in Express Transit mode in an iPhone's wallet feature. Express mode has been designed with commuters in mind, when they may want to quickly tap and pay at a turnstile to access rail, for example, rather than hold up a line due to the need to go through further identity authentication. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Apple released updates to iOS, iPad OS, and macOS after researchers from Toronto's Citizen Lab found a dangerous, hidden exploit buried in iMessage's code.
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Apple released security updates for older iPhones to fix a zero-day vulnerability tracked as CVE-2023-41064 that was actively exploited to infect iOS devices with NSO's Pegasus spyware.
CVE-2023-31064 is a remote code execution flaw that is exploited by sending maliciously crafted images via iMessage. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
The "rapid" security fixes are designed to quickly patch security flaws under active exploitation by hackers. Apple on Monday released its first batch of publicly available “rapid security” patches, aimed at quickly fixing security vulnerabilities that are under active exploitation or pose significant risks to its customers.
According to a notice, the so-called Rapid Security Response updates “deliver important security improvements between software updates.”
Rapid Security Responses were introduced to allow Apple customers to update their devices faster than a typical software update takes. Apple says the feature is enabled by default, and some rapid patches can be installed without rebooting, though not always. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Last week, we warned about the appearance of two critical zero-day bugs that were patched in the very latest versions of macOS (version 13, also known as Ventura), iOS (version 16), and iPadOS (version 16).
Zero-days, as the name suggests, are security vulnerabilities that were found by attackers, and put to real-life use for cybercriminal purposes, before the Good Guys noticed and came up with a patch. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
A new information-stealing malware has set its sights on Apple's macOS operating system to siphon sensitive information from compromised devices.
Dubbed MacStealer, it's the latest example of a threat that uses Telegram as a command-and-control (C2) platform to exfiltrate data. It primarily affects devices running macOS versions Catalina and later running on M1 and M2 CPUs.
"MacStealer has the ability to steal documents, cookies from the victim's browser, and login information," Uptycs researchers Shilpesh Trivedi and Pratik Jeware said in a new report. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=MacStealer

|
Scooped by
Gust MEES
|
Apple has just released updates for all supported Macs, and for any mobile devices running the very latest versions of their respective operating systems.
In version number terms:
iPhones and iPads on version 16 go to iOS 16.3.1 and iPadOS 16.3.1 respectively (see HT213635).
Apple Watches on version 9 go to watchOS 9.3.1 (no bulletin).
Macs running Ventura (version 13) go to macOS 13.2.1 (see HT213633).
Macs running Big Sur (version 11) and Monterery (12) get an update dubbed Safari 16.3.1 (see HT213638).
Oh, and tvOS gets an update, too, although Apple’s TV platform confusingly goes to tvOS 16.3.2 (no bulletin). Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Une nouvelle version du malware Dridex cible actuellement les Mac pour se propager sur un grand nombre d'ordinateurs.
Le malware Dridex est déjà connu par les utilisateurs de PC Windows, mais c'est la première fois que ce logiciel malveillant s'attaque à macOS. Pour ce faire, les hackers ont changé le mode de fonctionnement pour parvenir à leurs fins. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
The latest raft of non-emergency Apple security updates are out, patching a total of 87 different CVE-rated software bugs across all Apple products and plaforms.
There are 10 security bulletins for this bunch of updates, as follows:
APPLE-SA-2022-03-14-1: iOS 15.4 and iPadOS 15.4 (HT213182)
APPLE-SA-2022-03-14-2: watchOS 8.5 (HT213193)
APPLE-SA-2022-03-14-3: tvOS 15.4 (HT213186)
APPLE-SA-2022-03-14-4: macOS Monterey 12.3 (HT213183)
APPLE-SA-2022-03-14-5: macOS Big Sur 11.6.5 (HT213184)
APPLE-SA-2022-03-14-6: Security Update 2022-003 Catalina (HT213185)
APPLE-SA-2022-03-14-7: Xcode 13.3 (HT213189)
APPLE-SA-2022-03-14-8: Logic Pro X 10.7.3 (HT213190)
APPLE-SA-2022-03-14-9: GarageBand 10.4.6 (HT213191)
APPLE-SA-2022-03-14-10: iTunes 12.12.3 for Windows (HT213188) Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Apple addressed a new WebKit zero-day affecting iOS, iPadOS, macOS, and Safari that may have been actively exploited in the wild.
Apple has addressed a zero-day vulnerability, tracked as CVE-2022-22620, in the WebKit affecting iOS, iPadOS, macOS, and Safari that may have been actively exploited in the wild.
This is the third zero-day vulnerability fixed by the IT giant this year.
The flaw is a use after free issue that could be triggered by processing maliciously crafted web content, leading to arbitrary code execution
“Processing maliciously crafted web content may lead to arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited.” reads the security advisory published by Apple. “A use after free issue was addressed with improved memory management.”
The vulnerability was reported by an anonymous researcher, the company addressed it by improving the memory management.
Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Patch alert: You’re going to want to run—not walk—to your iPhone and iPad to update them right now.
A recently discovered vulnerability in Apple’s Safari web browser, CVE-2022-22594, could spill sensitive personal data, but you can patch it now by updating to Apple’s recently released iOS 15.3 and iPadOS 15.3, which were put out today.
The bug in question in is in Safari 15 and can actually leak your recent browsing history as well as personal identifiers, such as your Google User ID. The bug was discovered by researchers with security firm FingerprintJS, who found that a bug in Safari’s application of the IndexedDB API “lets any website track your internet activity and even reveal your identity.” Not a particularly fun thing to have happen. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Safari

|
Scooped by
Gust MEES
|
It’s been a wild few weeks for Apple, or perhaps an “in-the-wild” few weeks, with several zero-day bugs necessitating emergency updates.
We were going to say “unexpected updates”, but all (or almost all) Apple security patches are, of course, unexpected by design.
Apple deliberately announces security fixes only after they’ve been published, so you couldn’t plan for them even if you wanted.
Apple claims that this is for “customers’ protection”, because it prevents crooks who may have heard rumours about a security hole but haven’t figured it our for themselves from working out where to start looking for it.
On the other hand, it also means that you will hardly ever hear about official workarounds or threat mitigations from Apple, even if those workarounds might keep you safe during the gap between the zero-day hole appearing and the patch being created, tested and released.
Remember that zero-day vulnerabilities refer to bugs that cybercriminals know how to exploit before a patch is available, with the result that even a well-informed user or sysadmin would have had zero days to get officially ahead of the Bad Guys.

|
Scooped by
Gust MEES
|
Security researchers disclosed today a new vulnerability in Apple's macOS Finder, which makes it possible for attackers to run arbitrary commands on Macs running any macOS version up to the latest release, Big Sur.
Zero-days are publicly disclosed flaws that haven't been patched by the vendor which, in some cases, are also actively exploited by attackers or have publicly available proof-of-concept exploits.
The bug, found by independent security researcher Park Minchan, is due to how macOS processes inetloc files, which inadvertently causes it to run any commands embedded by an attacker inside without any warnings or prompts. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
|



 Your new post is loading...
Your new post is loading...






























Apple released emergency security updates to fix two new zero-day vulnerabilities exploited in attacks targeting iPhone and Mac users, for a total of 13 exploited zero-days patched since the start of the year.
"Apple is aware of a report that this issue may have been actively exploited," the company revealed in security advisories describing the security flaws.
The bugs were found in the Image I/O and Wallet frameworks and are tracked as CVE-2023-41064 (discovered by Citizen Lab security researchers) and CVE-2023-41061 (discovered by Apple).
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security