 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Apple has released Security Update 2015-003 for OS X Yosemite v10.10.2 to address multiple vulnerabilities. Exploitation of one of these vulnerabilities may allow a remote attacker to take control of an affected system. US-CERT encourages users and administrators to review Apple Security Update 2015-003 and apply the necessary updates.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
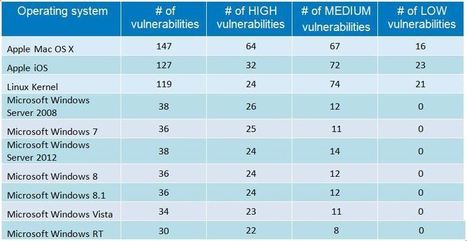
An average of 19 vulnerabilities per day were reported in 2014, according to the data from the National Vulnerability Database (NVD). In this article, I look at some of the trends and key findings for 2014 based on the NVD’s database. . #Mac OS X and #Linux had more #vulnerabilities in 2014 than ALL #Windows Versions in sum. .
Not surprisingly at all, web browsers continue to have the most security vulnerabilities because they are a popular gateway to access a server and to spread malware on the clients. Adobe free products and Java are the main challengers but web browsers have continuously topped the table for the last six years. Mozilla Firefox had the most vulnerabilities reported in 2009 and 2012; Google Chrome in 2010 and 2011; Internet Explorer was at the top for the last two years. To keep systems secure, it is critical that they are fully patched. IT admins should focus on (patch them first): - Operating systems (Windows, Linux, OS X)
- Web browsers
- Java
- Adobe free products (Flash Player, Reader, Shockwave Player, AIR).
. Learn more:

|
Scooped by
Gust MEES
|
Major cyber security incidents continue to hit the headlines. Security and privacy are top concerns for IT and security professionals, especially after 2014’s highly publicized data breaches.
Companies around the globe were victim to malware, stolen data and exploited vulnerabilities. Big companies weren’t immune to this, with Target, JPMogan Chase, Home Depot and Sony Pictures suffering the painful sting of data breaches. Even celebrities were targeted, with compromised iCloud accounts.
It really isn’t surprising that almost everyone anticipates the need to prepare for security challenges in the coming months. According to a recent survey by Tech Pro Research, 84 percent of IT professionals are more concerned about security and privacy in 2015.

|
Scooped by
Gust MEES
|
Apple is pushing out a mandatory update for Adobe Flash in the wake of the recent disclosure of three zero-day vulnerabilities that are actively being exploited in the wild.
Mac OS X will find that Flash has been disabled on their devices and will see popup messages urging them to install the latest updates if they want to continue to use the software.
“If you’re using an out-of-date version of the Adobe Flash Player plug-in, you may see the message ‘Blocked plug-in’, ‘Flash Security Alert’ or ‘Flash out-of-date’ when attempting to view Flash content in Safari. To continue viewing Flash content, update to a later version of Adobe Flash Player. Click the Download Flash button. Safari opens the Adobe Flash Player page on the Adobe website,” the advisory from Apple stated.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
|

|
Scooped by
Gust MEES
|
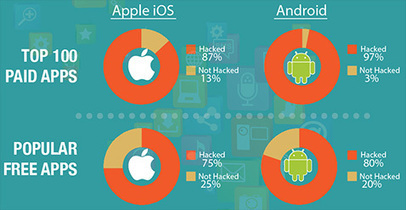
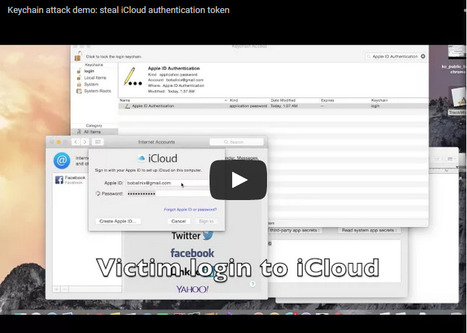
It’s become almost axiomatic that Apple devices and the apps on them are more secure than the competition. But researchers continue to blow up that notion and today a group of academics have ripped apart the securityprotections in Mac OS X and iOS to show it’s not only possible to create malware and get it onto the App Store, but it’s also feasible to launch “devastating” attacks using rogue software to steal the most sensitive personal data around, from iCloud passwords and Evernote notes to dodgy selfies and more.
The attacks, known as unauthorized cross-app resource access or XARA, expose design flaws that allow a bad app to access critical pieces of data in other apps. As a result, Apple has struggled to fix the issues, according to apaper released today from Indiana University Bloomington, Peking University and the Georgia Institute of Technology.
En savoir plus / Merhr erfahren / Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?tag=XARA

|
Scooped by
Gust MEES
|
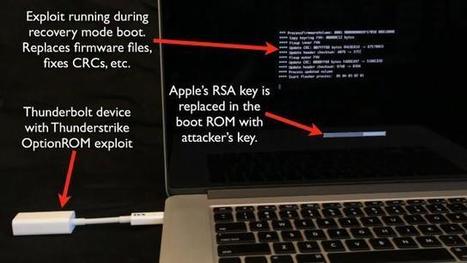
“It means that you can overwrite the contents of your BIOS from userland a rootkit EFI without any other tricks other than a suspend-resume cycle, a kernel extension, flashrom, and root access.
“The bug can be used with a Safari or other remote vector to install an EFI rootkit without physical access [provided] a suspended happens in the current session … you could probably force the suspend and trigger this, all remotely. That’s pretty epic ownage.”
Apple has been contacted for comment.
Flash locks are removed when machines enter a sleep state for about 30 seconds or more, allowing attackers to update the flashrom contents from userland including EFI binaries.
Affected models include the MacBook Pro Retina, and Pro, and MacBook Airs, each running the latest EFI firmware updates.
Some of the latest machines are not affected leading Vilaça to think Apple is aware of the vulnerability.
“If they (Apple) indeed knew about the bug – because I don’t believe it’s a coincidence not working in latest machines – then they keep their pattern of not patching older versions,” he says.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
At least 25,000 iOS apps available in Apple's App Store contain a critical vulnerability that may completely cripple HTTPS protections designed to prevent man-in-the-middle attacks that steal or modify sensitive data, security researchers warned.
1,500 IOS APPS HAVE HTTPS-CRIPPLING BUG. IS ONE OF THEM ON YOUR DEVICE?
Apps downloaded two million times are vulnerable to trivial man-in-the-middle attacks.
As was the case with a separate HTTPS vulnerability reported earlier this week that affected 1,500 iOS apps, the bug resides in AFNetworking, an open-source code library that allows developers to drop networking capabilities into their iOS and OS X apps. Any app that uses a version of AFNetworking prior to the just-released 2.5.3 may expose data that's trivial for hackers to monitor or modify, even when it's protected by the secure sockets layer (SSL) protocol. The vulnerability can be exploited by using any valid SSL certificate for any domain name, as long as the digital credential was issued by a browser-trusted certificate authority (CA).

|
Scooped by
Gust MEES
|
What was fixed?
The list of software components fixed in the various updates is extensive.
Rather than go into all the details, we'll just encourage you towards grabbing the updates by pointing out that the holes fixed include:
Remote code execution (RCE). Opening a booby-trapped file or browsing to a malicious web page could lead to implanted malware, stolen data and a hijacked computer. . Security bypasses. Files you might expect to be kept away from prying eyes might be visible; secrets useful for further attacks (such as memory addresses used by the operating system) might be revealed.
Denial of service. A crook could force your computer to shut down without warning. .
Data leakage. Passwords, private browsing data and application screenshots could be revealed. . Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
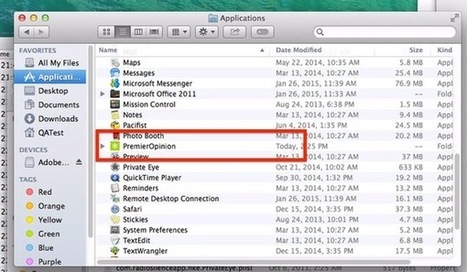
Almost five years ago, Intego security researchers warned about the OSX/OpinionSpy spyware infecting Mac computers, downloaded during the installation of innocent-sounding applications and screensavers distributed via well-known sites such as MacUpdate and VersionTracker.
Once compromised, infected Macs could leak data and open a backdoor for further abuse.
Now, sadly, a variant of OpinionSpy seems to be making something of a comeback.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Woburn, MA – February 10, 2015 - According to the Consumer Security Risk Survey conducted by Kaspersky Lab and B2B International, Apple users responded to have encountered cyber threats almost as often as the users of other platforms. The survey showed that 24 percent of Apple desktop users and 10 percent of Apple laptop users encountered malware during the year*, whereas the number of affected PC owners is slightly higher at 32 percent.
Although security experts have not, thus far, found as much harmful software for OS X as they have for other platforms like Windows, malware does still aim to attack Mac devices. Malware such as ransomware was reportedly faced by 13 percent of Mac users compared to 9 percent of Windows users. There is a similar situation with threats targeting financial data: these incidents were reported by 51 percent of OS X users and 43 percent of Windows users.
In addition the survey results showcased that Mac users are generally less aware of Internet threats than Windows users. For example, 39 percent of MacBook owners have never or hardly heard of ransomware, and 30 percent do not know about dangerous malicious programs that can exploit vulnerabilities in software. By comparison, among all respondents 33 percent know almost nothing about ransomware and 28 percent are unaware of exploits.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Adobe has released Flash Player 16.0.0.305, a new version that fixes the latest zero-day flaw (CVE-2015-0313) that is currently exploited in...

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
|



 Your new post is loading...
Your new post is loading...





















Learn more:
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?tag=Thunderstrike